English translations
This post was translated with the help of a translation tool. Therefore, occasional errors are possible. An error-free version is available in German

This page is also available in:
Deutsch (German)
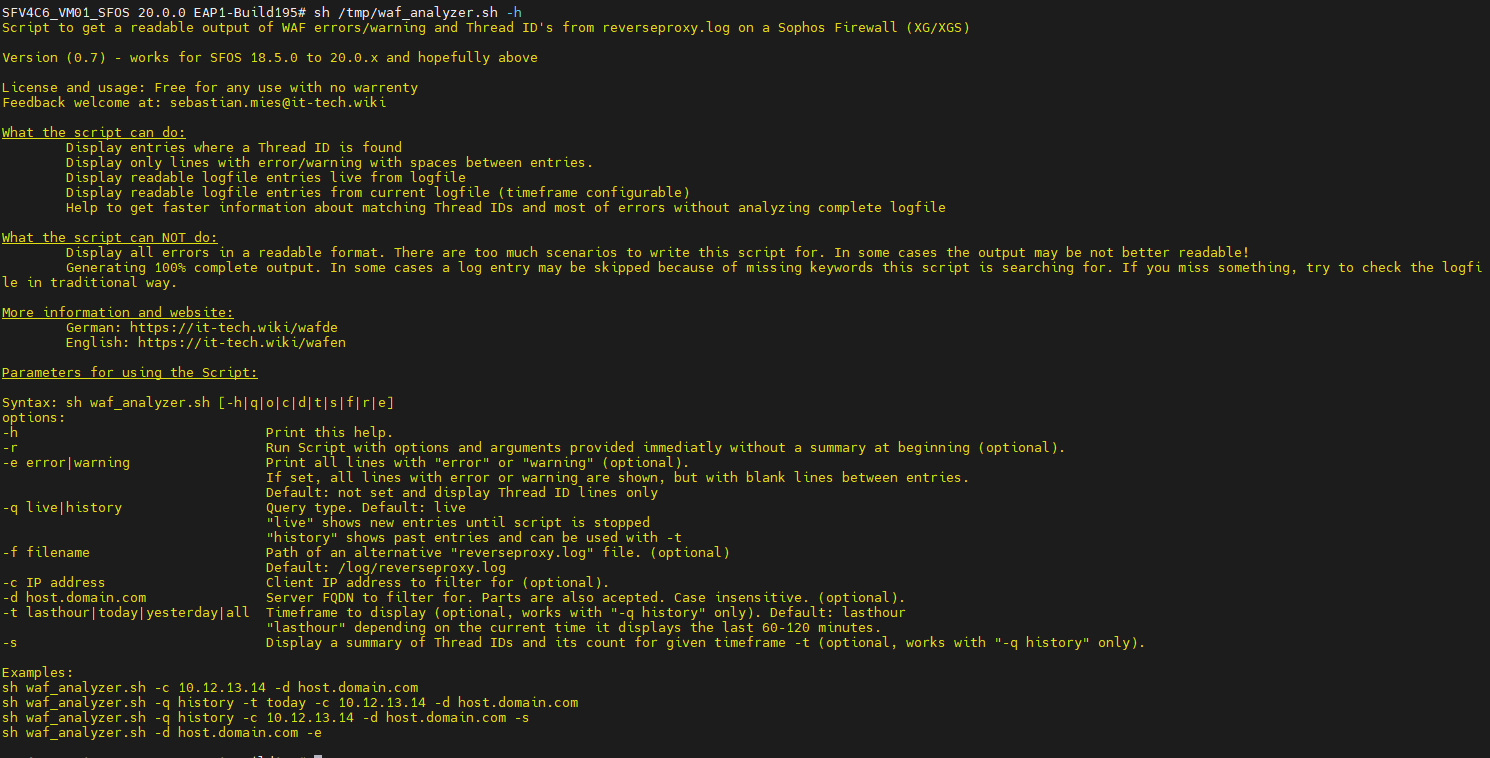
A Sophos Firewall reverseproxy.log analysis script which helps to analyze errors and find thread IDs in the reverseproxy.log file. The thread IDs found are displayed in a quickly readable format.
Anyone who has ever set up a WAF on the Sophos firewall will know that finding thread IDs is extremely tedious. As I regularly configure WAFs for my customers, the collection of shell commands in my collection was getting longer and longer. A more practical solution was needed. Especially as the output was still difficult to read. From this, the Sophos Firewall reverseproxy.log analysis script offered here was born.
Read on and find out what the script can - or cannot - do.
Have fun analyzing! 😀
This script does not make any changes to the system. However, as always, caution is advised when using the shell. If you have no experience in using the shell, please ask for support here in the comments or contact your Sophos partner.
We assume no responsibility for errors that may occur when using the script. Use at your own risk and should always be done in a test environment first.
The following requirements must be met in order to use the script:
The script can evaluate the following information and display it in a readable format:
The script cannot do the following:
The script can be controlled via several parameters. In general, the script is started as follows if it is located in the /tmp directory.
sh /tmp/waf_analyzer.shWithout parameters, the file "/log/reverseproxy.log" is evaluated and the thread IDs are displayed live. There is no filtering according to the client IP or the server FQDN.
-h
Displays help on the parameters.
-c 169.254.254.254
Filters according to the source IP address and only outputs matching lines.
The parameter is optional.
-d demo.it-tech.wiki
Filters by FQDN of the WAF and only outputs matching lines.
Upper and lower case is not important.
It is also possible to search only for parts of the FQDN. E.G.: -d it-tech
The parameter is optional - but mandatory for "-s".
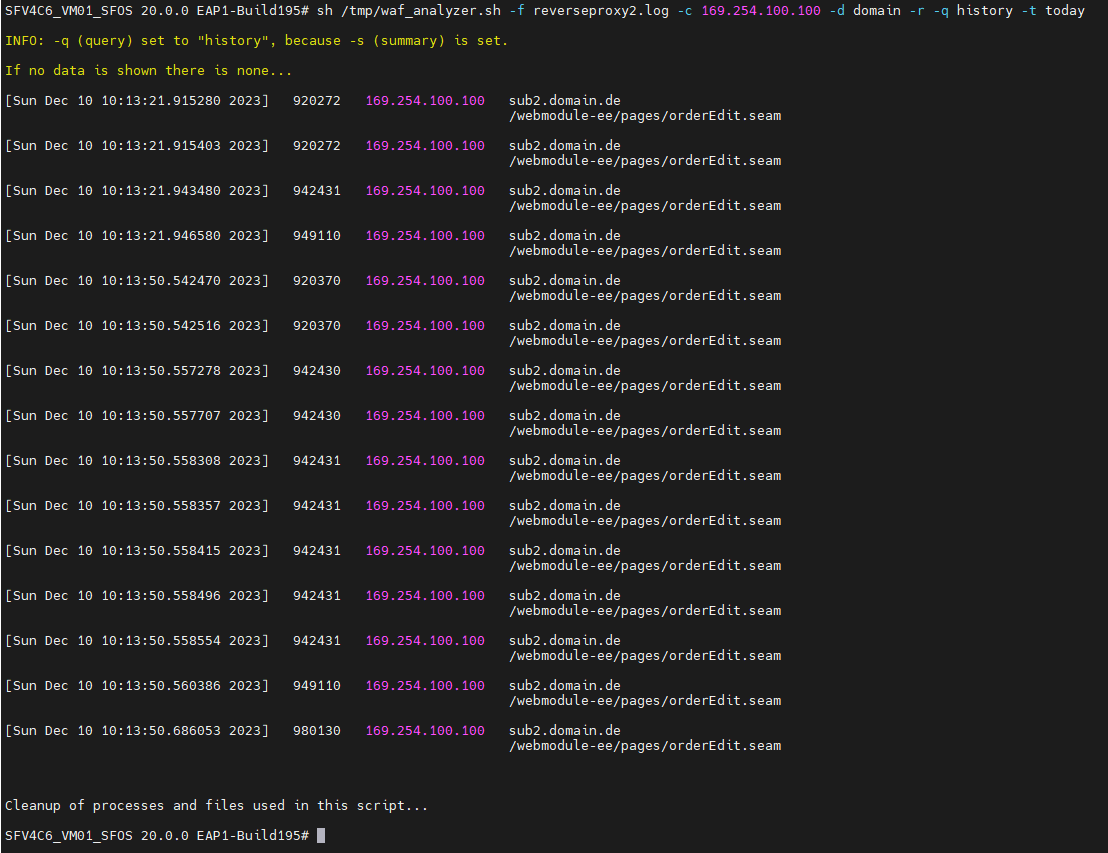
-q history
Instead of new data (live), the old data can be displayed.
The parameter is optional and can be combined with "-t". If "-t" is not specified, "-t lasthour" is set.
-t lasthour
Possible values are:
- "lasthour" = the last 60-120 minutes (depending on the current time)
- "today" = everything from the current day
- "yesterday" = everything from yesterday
- "all" = all data contained in the log file
The parameter is required for "-q history". If it is not set, "lasthour" is set.
Can be combined with all parameters.
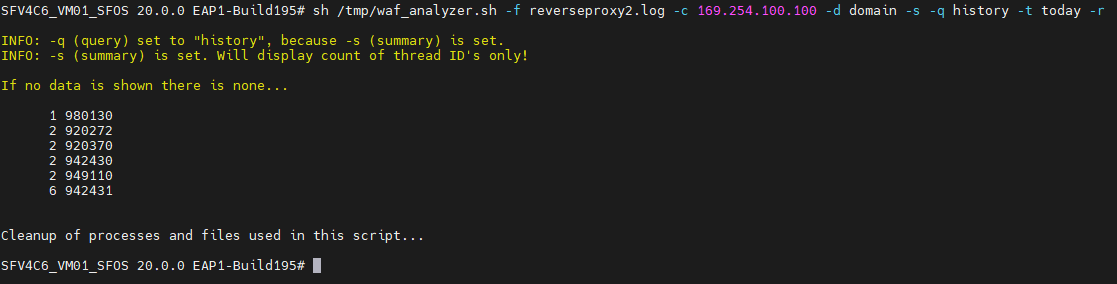
-s
Displays the frequency of occurrence of thread IDs in the time period of the "-t" parameter. If -t is not set, "lasthour is set".
The parameter "-d domain" is also required.
The parameter is optional.
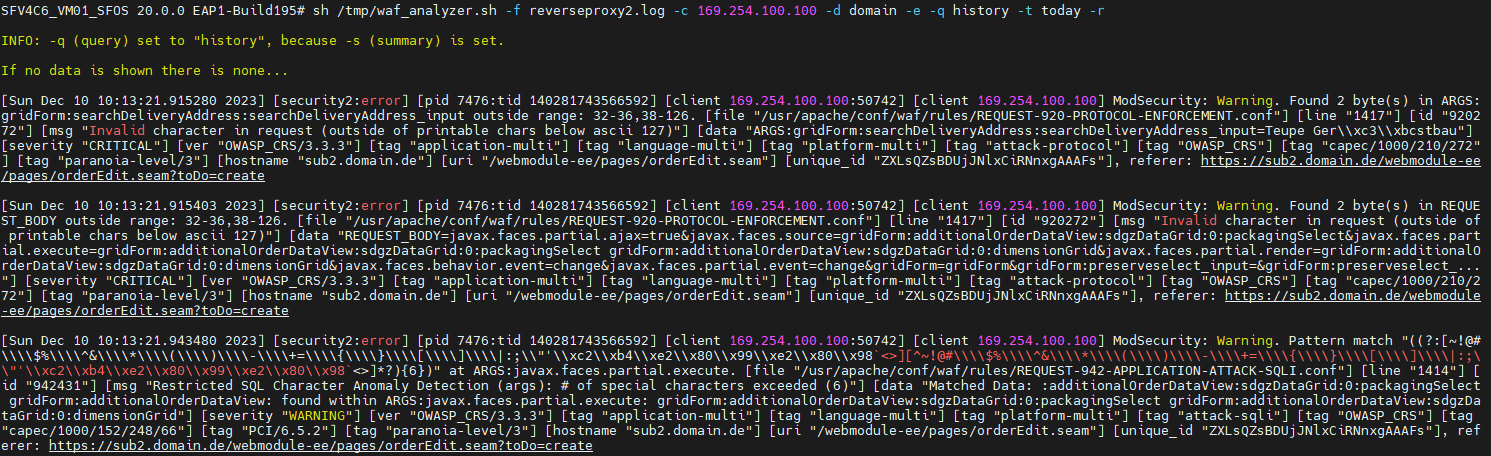
-e
This parameter is not used to evaluate the thread IDs. All lines containing the word "error" or "warning" are output. An empty line is output between the entries for better readability.
Can be combined with -c, -d, -q, -t
The parameter is optional.
-f /tmp/otherlog.log
If a log file other than "/log/reverseproxy.log" is to be used, this can be set with this parameter.
The parameter is optional.
-r
By default, the script outputs a small summary of the parameters and the command line to be executed before execution and then starts after 5 seconds.
With -r this is skipped and the output starts directly.
The parameter is optional.
The easiest way is to call the following command on the advanced shell. The "Installer" loads the current version into the /tmp directory and renames any old versions of the script. The script can then be used directly.
curl -L -s -o /tmp/install_waf_analyzer.sh https://it-tech.wiki/wafinstaller && sh /tmp/install_waf_analyzer.sh && rm /tmp/install_waf_analyzer.shIf you prefer to load the script manually onto the firewall, you can download it here and place it on the firewall yourself.
For example, tools such as WinSCP can be used to upload to the Sophos Firewall.
This page is also available in:
Deutsch (German)
Feel free to leave a comment and share your opinion! This helps us to improve the tools and drive further exciting developments
This page is also available in:
Deutsch (German)
You're leaving the website
You are about to leave the website and are going to:
{fbExpr this.triggerElement.href}
Please make sure that you trust this website as we cannot be held responsible for external content.